Integrate a new JFrog Artifactory source
This integration leads to an automatic full scan of your monitored repositories. This implies an initial download of your Docker images, which may incur bandwidth costs with your Cloud Provider. To reduce these costs, while minimizing the risk of false positives, we recommend you to take advantage of the Filepath exclusion feature by adding this suggestion of filepaths to exclude from scanning.
Setting up and configuring this integration is limited to users with an Owner or Manager access level. JFrog Artifactory installation is only open to workspaces under the Business plan. However, you can install and test secret detection in JFrog Artifactory with a 30-day trial. Any secret incidents detected during the trial will remain accessible in your incident dashboard.
GitGuardian integrates natively with JFrog Artifactory via an Access Token that an administrator can create from your JFrog Artifactory instance. Note that GitGuardian only has read access to your repositories.
Setup your JFrog Artifactory integration
You can install GitGuardian on multiple JFrog Artifactory instances to monitor your repositories.
-
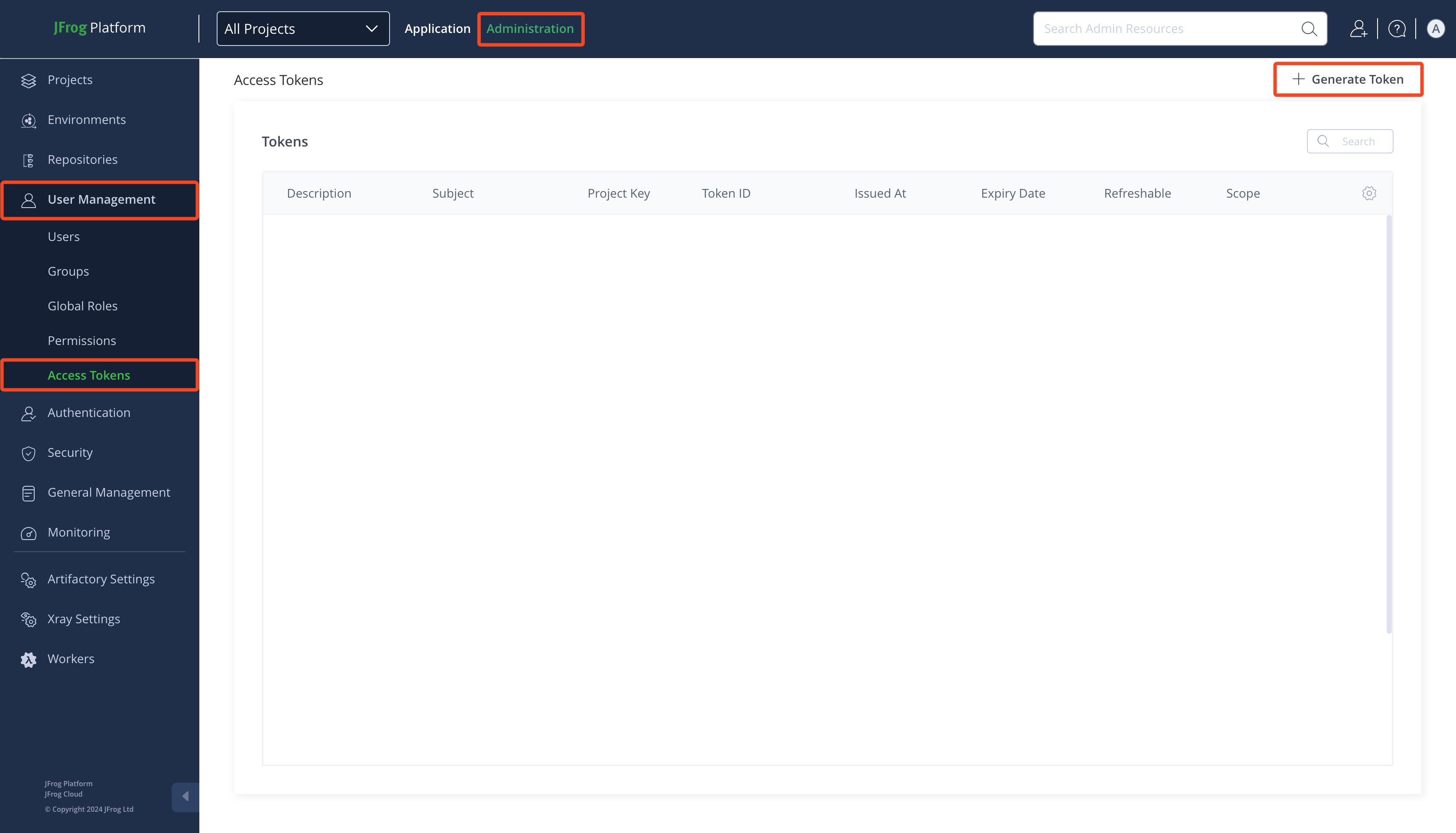
Make sure you're logged as an administrator in your JFrog Platform
-
Go to Administration > User Management > Access Tokens
-
Click Generate Token
-
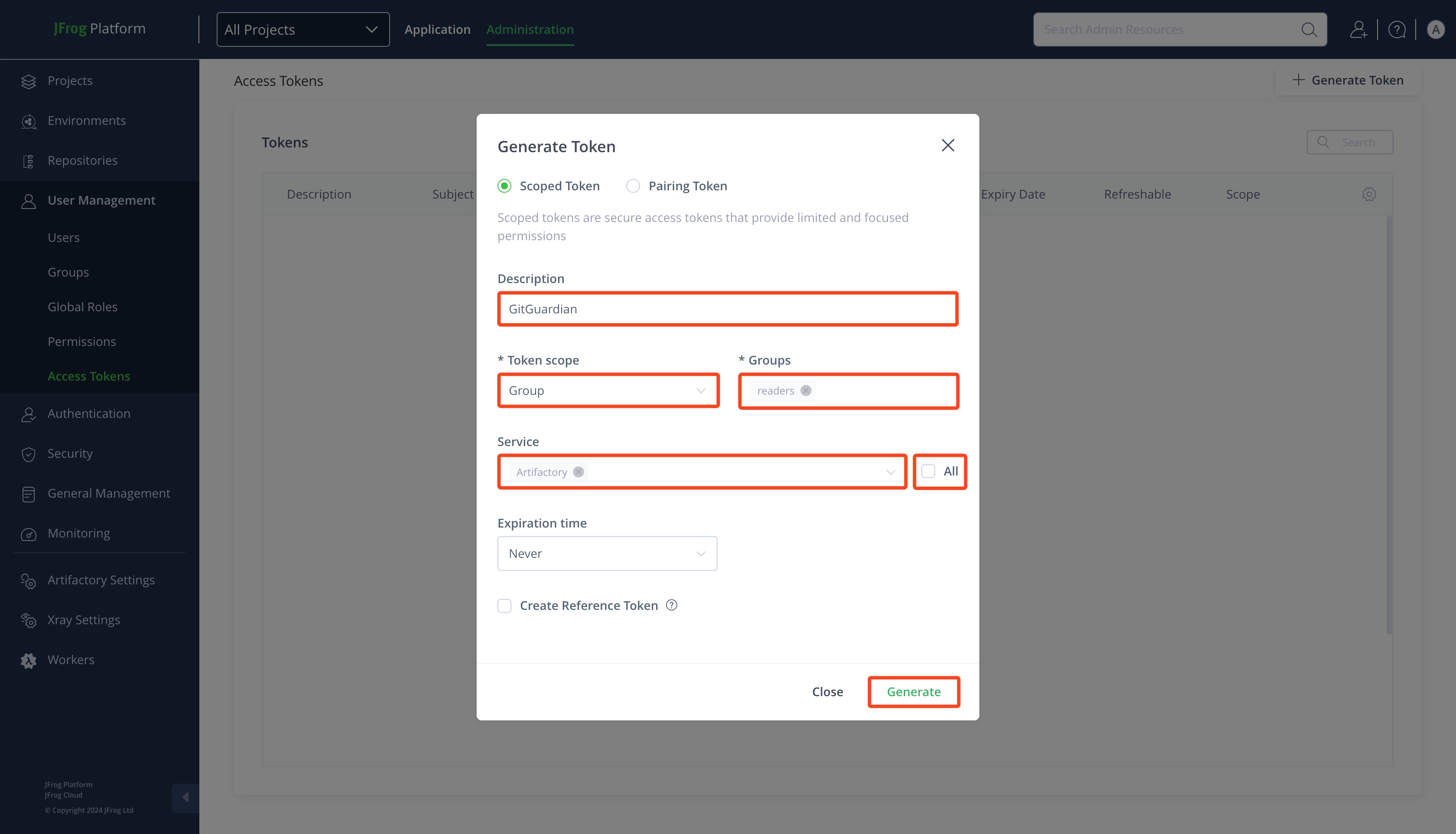
Type a Description (e.g.:
GitGuardian) -
Select
Groupas Token scope -
Select
readersas Groups -
Uncheck All and select
Artifactoryas Service -
Click Generate
-
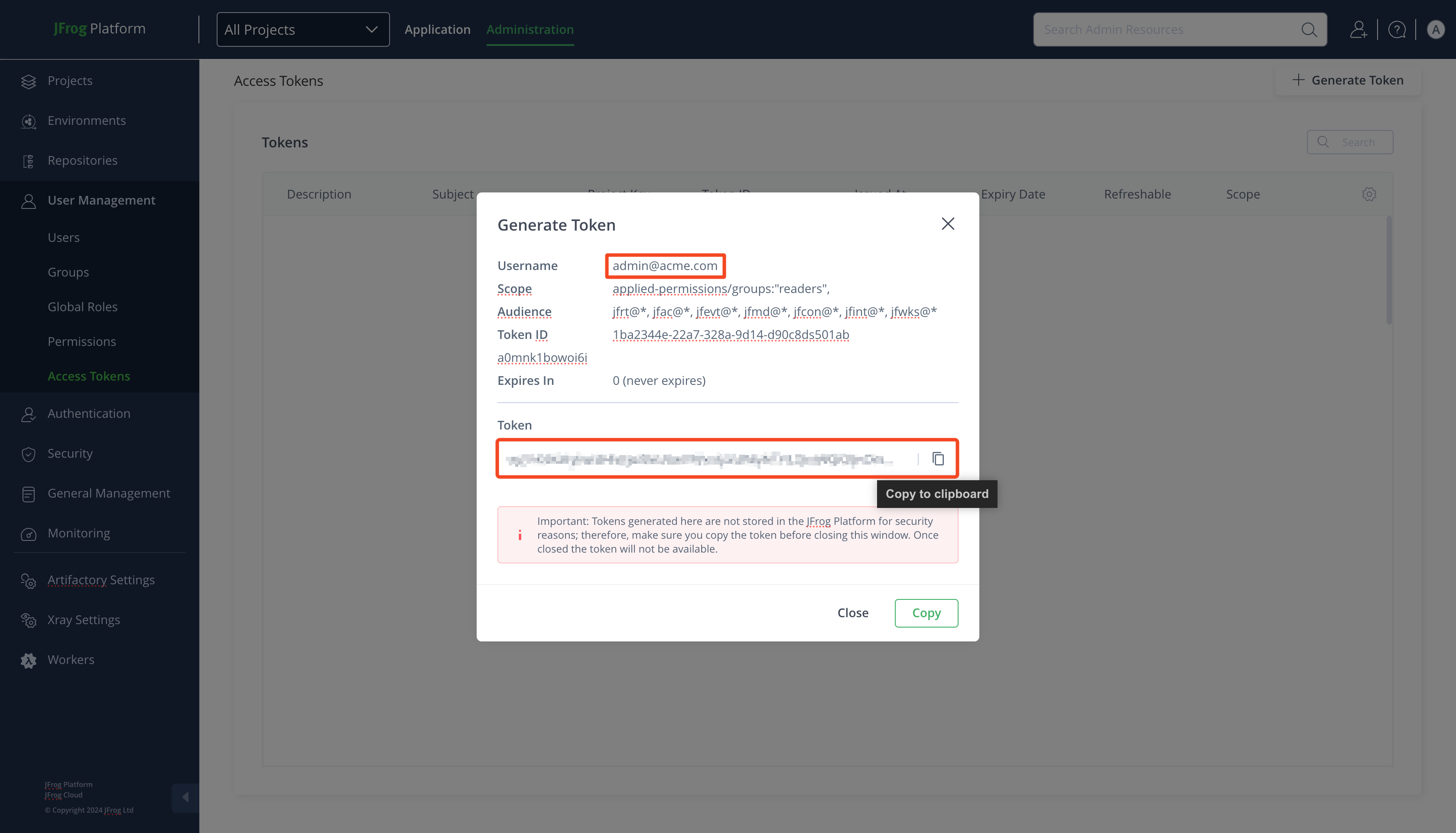
Get the Username and copy the Token
-
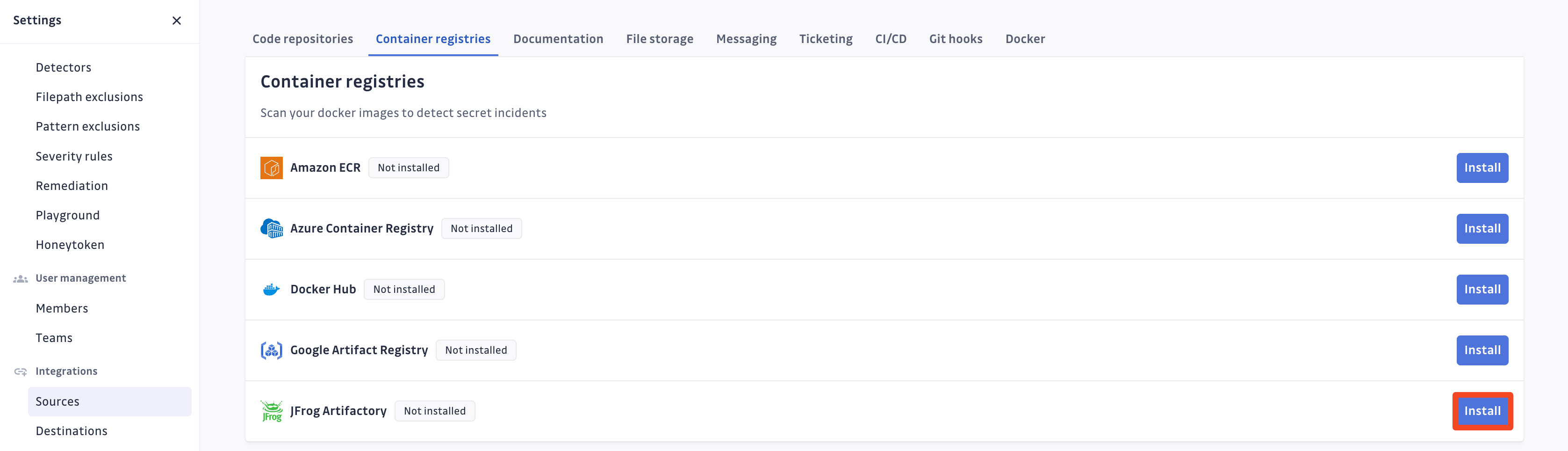
In the GitGuardian platform, navigate to the Sources integration page
-
Click Install next to JFrog Artifactory in the Container registries section
-
Click Install on the JFrog Artifactory integration page
-
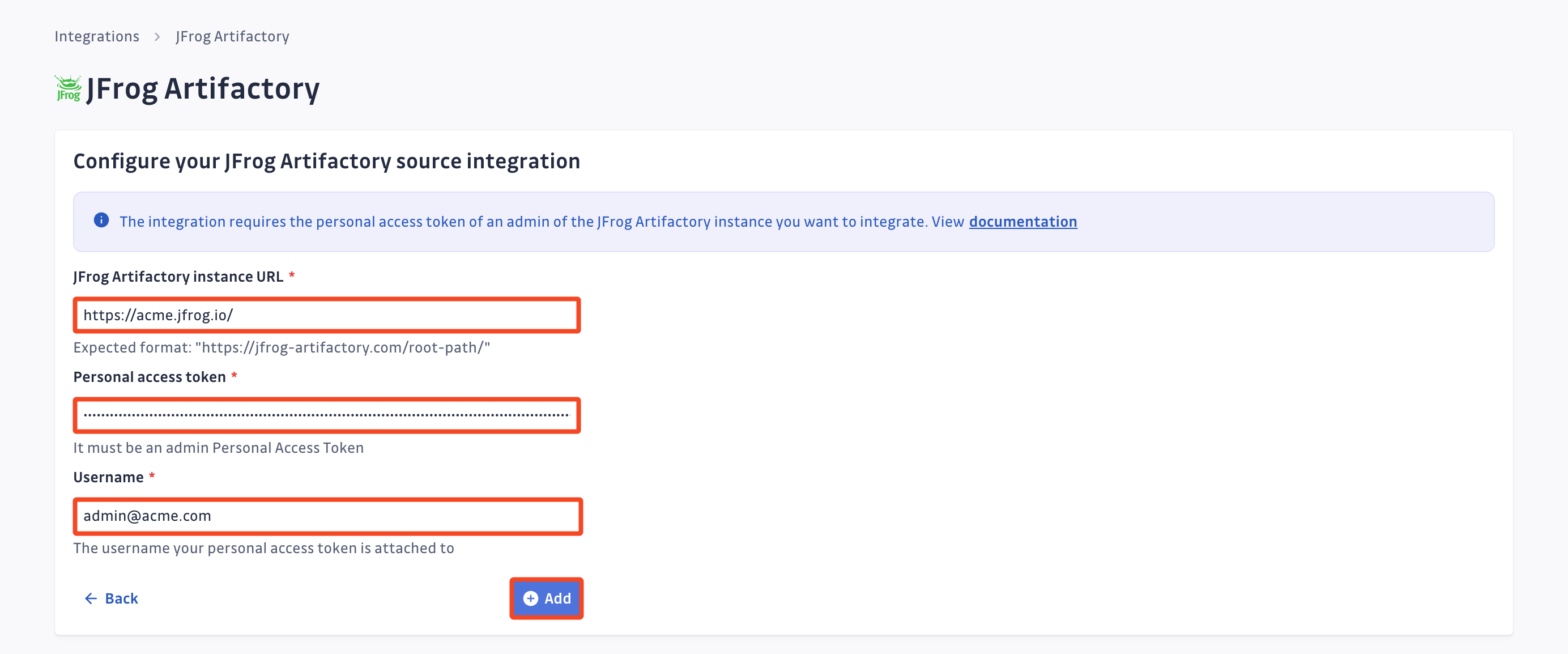
Type your JFrog Artifactory instance URL (e.g.:
https://acme.jfrog.io/) -
Paste your Personal access token
-
Type the associated Username (e.g.:
admin@acme.com) -
Click Add
-
Customize your monitored perimeter:
- Monitor specific JFrog Artifactory repositories (Recommended)
- No repositories are monitored by default, you will have to select them manually.
- Newly created repositories will not be monitored by default. You can adjust this setting at any time.
- Recommended to optimize your bandwidth costs.
- Monitor the entire JFrog Artifactory instance
- All repositories are monitored by default with a full historical scan automatically triggered.
- Newly created repositories will be monitored by default. You can adjust this setting at any time.
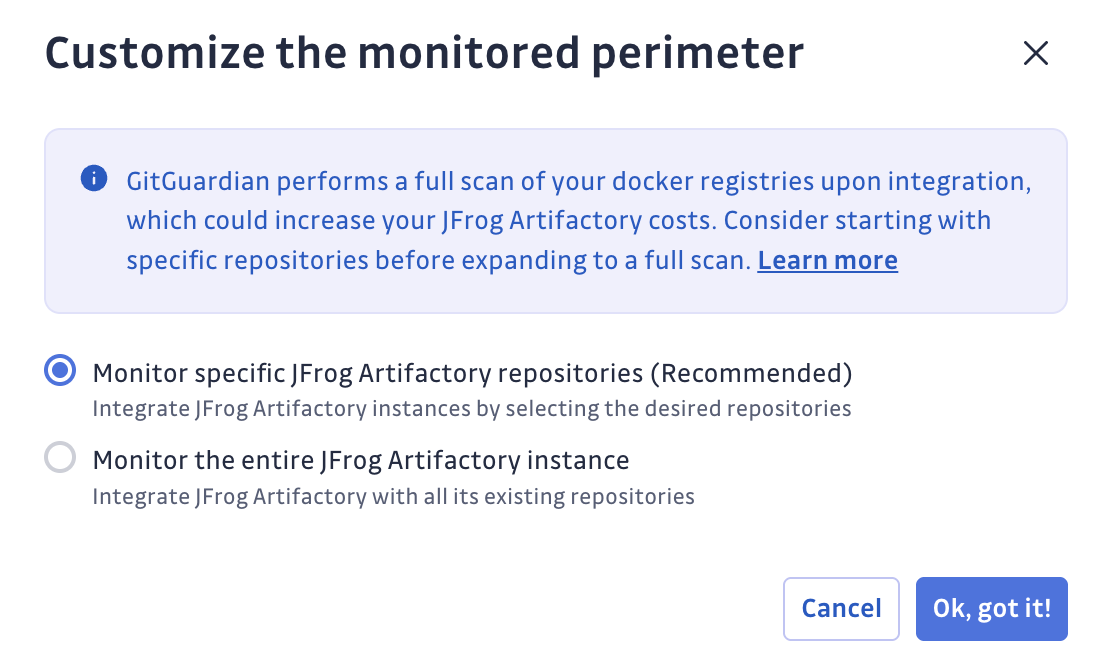
- Monitor specific JFrog Artifactory repositories (Recommended)
That's it! Your JFrog Artifactory instance is now installed, and GitGuardian is monitoring all Docker images of your selected repositories for secrets.
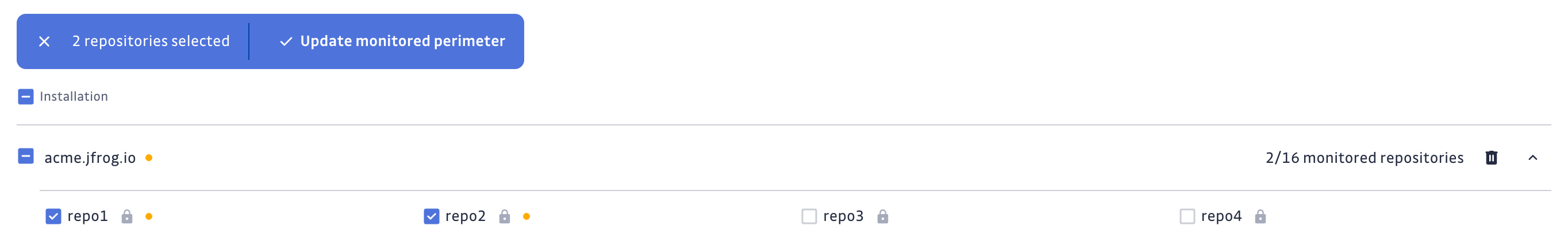
Customize your monitored perimeter
To customize the monitored repositories, navigate to your JFrog Artifactory settings.
- Select/Unselect repositories to include or exclude them from monitoring
- Confirm by clicking Update monitored perimeter
Automatic repository monitoring
You can enable or disable the automatic addition of newly created repositories to your monitored perimeter by switching the option in your JFrog Artifactory settings.

Uninstall your JFrog Artifactory instance
To uninstall a JFrog Artifactory instance:
- In the GitGuardian platform, navigate to the Sources integration page
- Click Edit next to JFrog Artifactory in the Container registries section
- Click the bin icon next to the JFrog Artifactory instance to uninstall
- Confirm by clicking Yes, uninstall in the confirmation modal
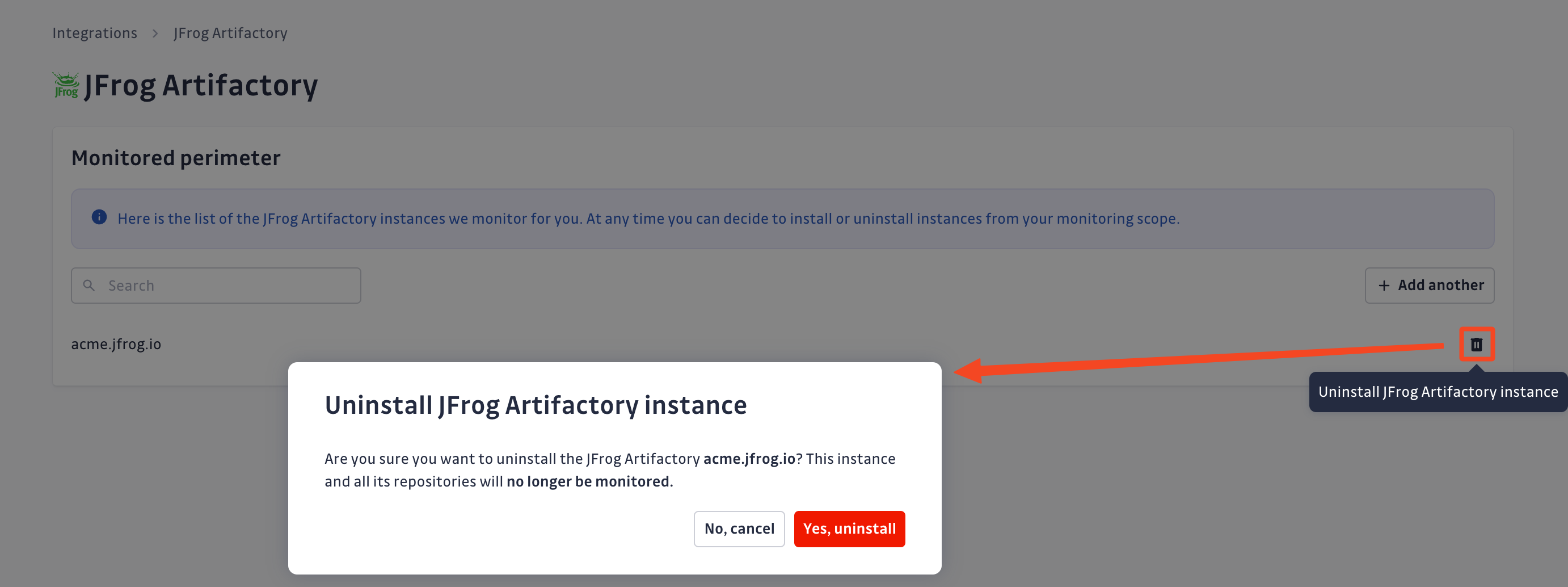
That's it! Your JFrog Artifactory instance is now uninstalled.
Excluded paths
GitGuardian automatically excludes files from scanning if their paths contain any of these regular expressions:
/__pypackages__/
/\.venv/
/\.tox/
/site-packages/
/venv/
distutils/command/register.py
python.*/awscli/examples/
python.*/dulwich/(tests|contrib/test_)
python.*/hgext/bugzilla.py
python.*/mercurial/util.py
python.*/test/certdata/
python.*/urllib/request\.py
python.*/pygments/lexers/
/cryptography.+/tests/.+(fixtures|test)_.+.py
/python.+pygpgme.+/tests/
botocore/data/.+/(examples|service)-.+.json
usr(/local)?/lib/python.+/dist-packages
/libevent.+/info/test/test/
/conda-.+-py.+/info/test/tests.+/test_.+\.py
/python[^/]+/test/
/man/man5/kdc\.conf\.5
erlang.*(inets|ssl).*/examples/
/gems/.*httpclient.*/(test|sample)/
/gems/.*faraday.*/
/vendor/bundle/
/\.gem/
/(g|G)o/src/cmd/go/internal/.*_test.go
/(g|G)o/src/cmd/go/internal/.*/testdata/
/(g|G)o/src/cmd/go/testdata/
/(g|G)o/src/crypto/x509/platform_root_key.pem
/(G|g)o/src/crypto/tls/.*_test.go
/(g|G)o/src/net/(url|http)/.*_test.go
src/github.com/DataDog/datadog-agent/.*test.*.go
google/internal/.*_test.go
golang.org.*oauth2@.*/.*.go
/flutter/.*/packages/flutter_tools/test/data/
/flutter/.*/examples/image_list/lib
/\.pub-cache
etc/ssl/private/ssl-cert-snakeoil\.key
perl.*Cwd.pm
ansible/.*/tests/(integration|unit)/
ansible/.*/test/awx
ansible/collections/ansible_collections/.*/plugins/
/curl/.*/(tests|docs|lib/url.c)
/doc/wget.+/NEWS
dist/awscli/examples/
usr(/local)?/lib/aws-cli/examples/
/google-cloud-sdk/(lib|platform)/
\.git/modules/third[-_]?party/
\.git/modules/external/
/\.npm/_cacache
/node_modules/
/\.parcel-cache/
/\.yarn/cache/
/\.m2/
/\.ivy2/cache/
/\.mix/
/\.hex/
/composer/cache/
/\.nuget/packages/
/libgpg-error/errorref\.txt
/Homebrew/Library/Taps/
/tcl[^/]+/http-.+.tm
Limitations
This integration is currently in beta and has the following limitations:
- Scan Frequency: Scans occur once a day. It may take several hours to detect newly leaked secrets.
For GitGuardian Self-Hosted instances, scan frequency can be configured in the Admin Area.- Time interval unit: seconds
- Default value: 86400 (1 day)
- Minimum value: 1800 (30 minutes)
- Team Perimeter: Customization of a team perimeter with JFrog Artifactory repositories is not supported. Users must be in All-incidents team to view and access JFrog Artifactory incidents.
- Source Visibility: The visibility of repositories is not determined. All repositories are considered
privatein both the UI and API. - Presence Check: The presence check feature is not supported. All occurrences are considered
presentin both the UI and API. - Occurrence Previews: Previews of occurrences are not supported.
Privacy
Country-specific laws and regulations may require you to inform your users that your repositories are being scanned for secrets. Here is a suggestion for a message you may want to use:
As part of our internal information security process, the company scans its repositories for potential secrets leaks using GitGuardian. All data collected will be processed for the purpose of detecting potential leaks. To find out more about how we manage your personal data and to exercise your rights, please refer to our employee/partner privacy notice. Please note that only repositories relating to the company’s activity and business may be monitored and that users shall refrain from sharing personal or sensitive data not relevant to the repository’s purpose.

