2026.5
| Version | |
|---|---|
| 2026.5.0 | May 21, 2026 |
| 2026.5.1 | May 28, 2026 |
System Requirements Update
Ensure your infrastructure meets the latest requirements for optimal performance and security:
| Component | Minimum Version | Recommended Version |
|---|---|---|
| KOTS | 1.117.3 | Latest |
| Kubernetes | 1.30 | 1.35 |
| PostgreSQL | 15 | 17 |
| Redis | 6 | 7 |
| ggscout | 0.19.0 | Latest |
Helm & Upgrade Considerations
To ensure compatibility, please review Helm values updates from the previous version. Air gap deployment? Find all the images and tag names in the air gap install page.
If you deploy GitGuardian through Argo CD with ServerSideApply=true, review the Hook Jobs may not be re-triggered on chart upgrade known issue before upgrading. Affected hook Jobs (pre-deploy migrations, post-deploy, upgrade-path-check, data-access-deploy) may silently skip — run argocd app sync gitguardian as a workaround.
Feature highlights
- Advanced Analytics enabled by default for Helm installation — actionable dashboards for detection, remediation, and prevention of secret leaks are now activated by default on all instances, including the new Analytics Overview page, previously available in early access, that aggregates KPIs across Protect, Detect, Remediate, and Govern in a single dashboard. Learn more.
Requires ~12 GB extra memory and increases database usage by 15-20% (min. 5-6 GB). Data refreshes once a day. KOTS installation must enable the new analytics in KOTS admin console.
- New AI workspace setting — workspace owners now have a self-service Settings → Workspace → AI page to enable or disable external LLM calls and configure Bring Your Own Cloud (BYOC) providers, with AWS Bedrock supported at launch. External LLM features are disabled by default on self-hosted instances. Once the integration is up and running, the selected Anthropic model powers every LLM-driven feature in the app. See AI settings and the AWS Bedrock setup guide.
- NHI admin and overprivileged flags — NHI Governance now flags admin-level and overprivileged non-human identities across AWS IAM, Microsoft Entra, and Okta, and automatically bumps the severity of any policy breach landing on an admin NHI. Learn more.
- Attachment scanning across Atlassian — secret detection now covers file attachments on Jira Cloud, Jira Data Center, Confluence Cloud, and Confluence Data Center. Reinstall your Atlassian integrations to grant the new attachment scopes. Learn more.
- New Slack capabilities — file attachment scanning, interactive thread responses (beta), and private channel name redaction. To enable them, add the latest Bot Token Scopes to your existing Slack app (no reinstall required). See the updated permissions list. Learn more.
Secrets Detection Engine
- v2.161 — 7 new detectors (Payhere App Credentials, HubSpot API Key, Birdeye API Key, Datadog API Credentials, Payhere Merchant Secret, GitGuardian Personal Access Token, GitGuardian Service Access Token), 1 new checker (Azure SignalR Connection String), 4 detector precision improvements (Jira Basic Auth, Atlassian OAuth2, npm Token, OpenWeatherMap Token), 5 new analyzers (Intercom Access Token, GitGuardian PAT/SAT, Notion Integration Token, Azure Cosmos DB Credentials).
- v2.162 — 16 new detectors (Aikido CI Scanning Token, Baidu AI API Key, Baidu Cloud API Keys, Bitrise Personal/Workspace Access Tokens, Canva Integration OAuth2, Cloudflare API Token V2, CockroachDB API Key, Coder Session Token, Datadog Application Key, ElevenLabs API Key, HashiCorp Consul ACL Token, MaxMind License Key, QQ Robot API Keys, Snyk Key V2, Volcengine API Key), 6 detector updates (Azure OpenAI, GitLab Token, Google Cloud Keys, Grafbase, PayPal Braintree, Slack Bot Token), 2 new analyzers (Azure AI Search Key, Azure OpenAI), 3 analyzer updates (Anthropic Admin Key, GitLab Token, PostgreSQL Credentials).
Enhancements
- Accessibility:
Ctrl+Enterto submit forms; dynamic variables (e.g.,{secretType},{sourceName},{sourceType}) now supported across all Jira integration fields. Learn more. - Deprecated Honeytoken Labels Public API removed (use Custom Tags), Jira templates flag unsupported required fields, GitHub Check runs reliability during partial outages. Learn more.
- Microsoft Teams notifications expanded to full incident lifecycle; new Public API Health Checks endpoints; archived-source filters on Sources and Incidents endpoints. Learn more.
- Microsoft Teams Issue Regression event backfilled for existing notifiers, leak author now captured on JFrog Artifactory incidents. Learn more.
- Self-Hosted:
- Improved the support bundle upload with a more descriptive filename (including hostname, date, and ticket ID and an instance ID display.
- Added
logCollector.supportBundle.logLevelto filter Loki queries when generating a support bundle. - Added dedicated
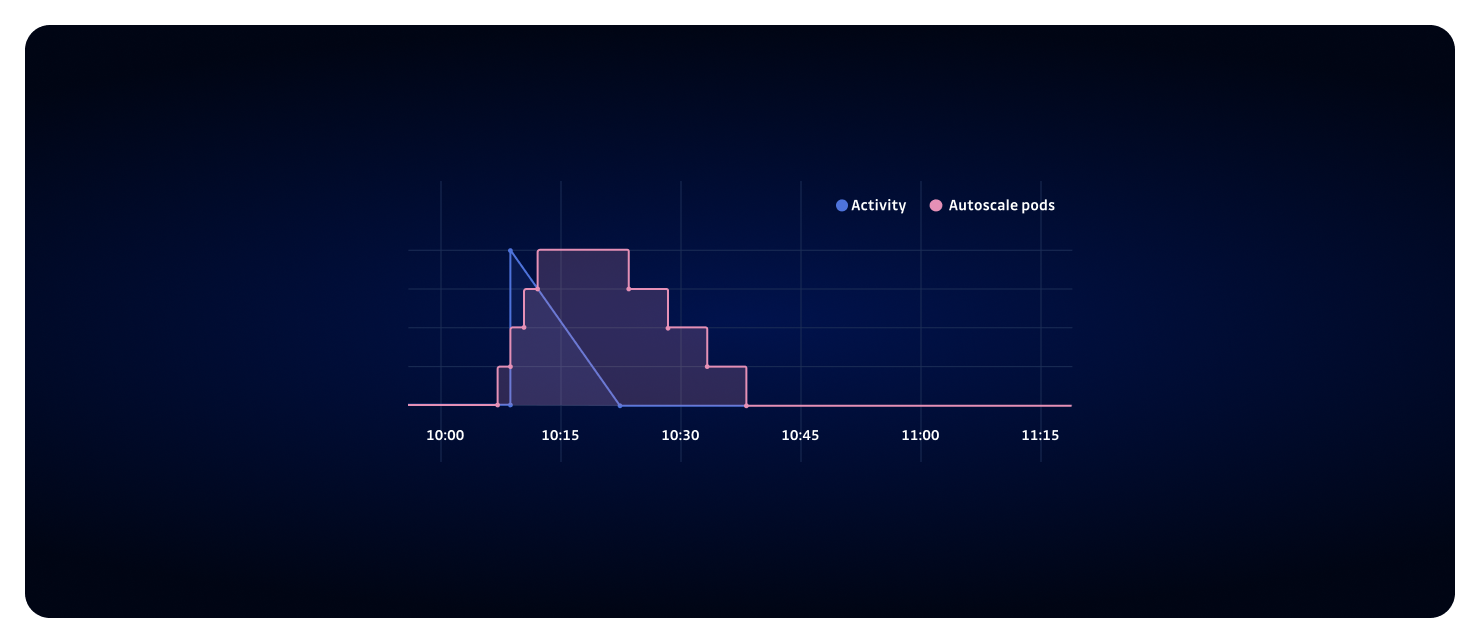
celeryWorkers.automatic-severitiesworker — moves theautomatic_severitiesqueue out of thelongworker into its own scalable worker. See the updated application topology. - Helm upgrades no longer fail when the chart is configured with a third-party cert-manager issuer plugin. The
certManagervalues schema now accepts plugin issuer kinds in addition to the built-inIssuerandClusterIssuer.
Fixes
- PAT source scopes not applied correctly, Bitbucket Cloud workspace-scoped APIs. Learn more.
- Dashboard unresponsive when filtering PATs, Bitbucket Cloud cross-workspace API deprecation handled. Learn more.
- SendGrid revocation error, JFrog Artifactory bulk select-all in team perimeters, GitHub Enterprise health check on GHES 3.19.4, GitHub Enterprise PR Check runs analytics dashboards, perimeter page rendering on workspaces with 200k+ sources. Learn more.
Hotfixes
2026.5.1
Release Date: May 28, 2026
Fixes
- Security: Fixed an XSS / open-redirect vulnerability via a crafted
redirect_urlquery parameter in the login and bulk-scan flows. - Jira Data Center: Fixed scan timeouts on large instances and improved handling of missing or null fields during scans.
- Machine Learning: Removed a test artifact from the ML Secret Engine image that was being flagged as a private key by container scanners.
- Self-Hosted: Bundled component bumps — Replicated SDK, MinIO (log collector), ML Secret Engine. See the air gap install page for the updated tags.