Red Hat Quay Integration: Your Enterprise Images, Under Watch
Release Date: March 5, 2026
Another registry, zero blind spots. We're expanding GitGuardian's container security coverage with a new integration for Red Hat Quay — the enterprise-grade, OCI-compliant registry trusted by organizations running OpenShift and hybrid cloud infrastructure.
Whether you're on quay.io or running a self-hosted Quay instance, GitGuardian now has you covered by scanning your container images for hardcoded credentials, API keys, and internal tokens buried in image layers.
What does this mean for you?
- SaaS and self-hosted, covered: Works with quay.io and on-premise Red Hat Quay deployments — same integration, same protection.
- Full image layer analysis: Every layer, every Dockerfile, every environment variable — scanned for secrets that shouldn't be there.
- Historical + incremental scanning: Catch secrets already hiding in existing images, and detect new ones as they're pushed.
- Granular perimeter control: Monitor specific repositories or your entire Quay instance — fine-tune coverage to match your needs.
- OAuth2 authentication: Secure, token-based integration with read-only access. No credentials stored, no write permissions required.
Why is this important?
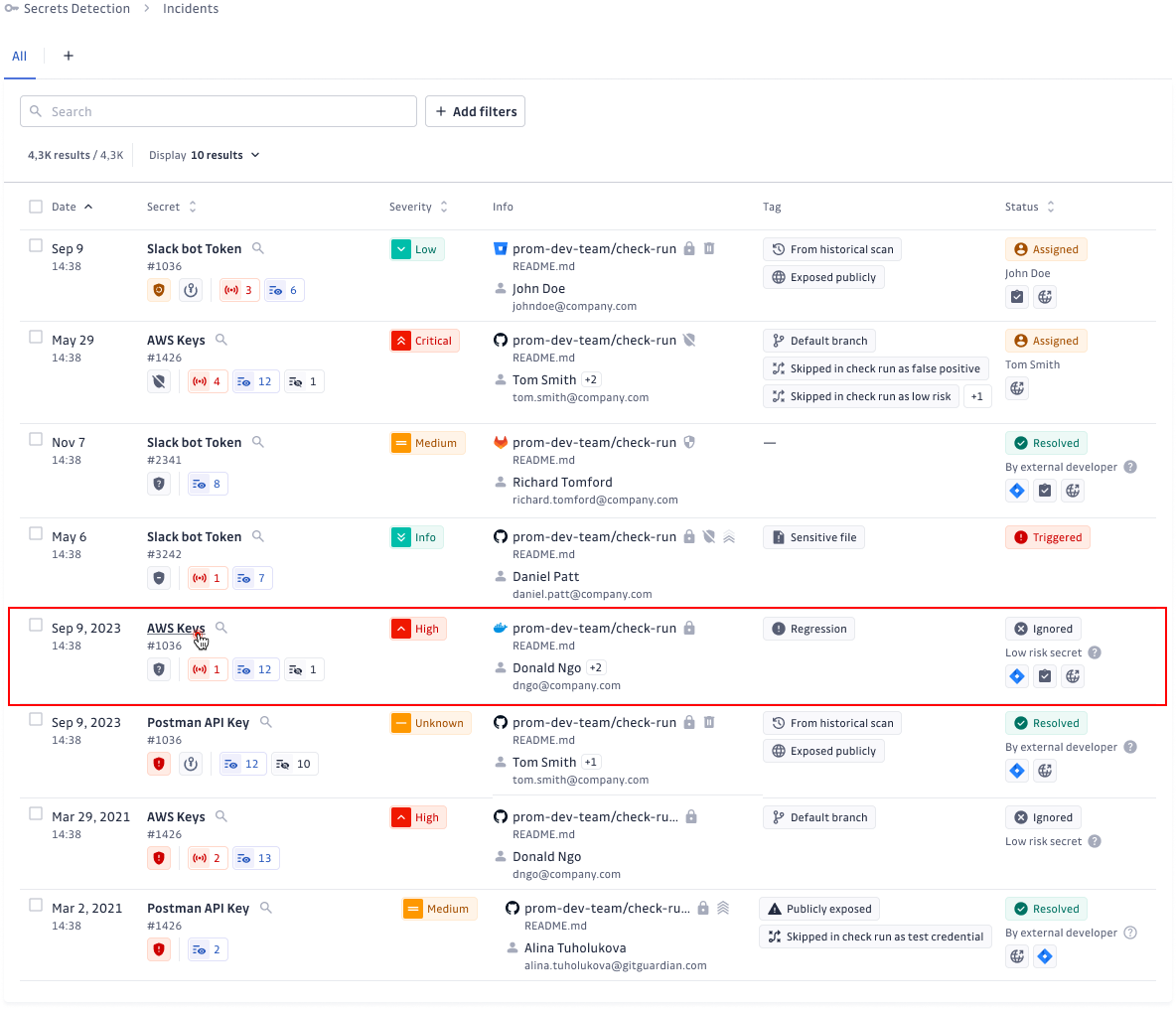
Container images are the final artifact before production. A secret embedded in an image layer — a database password in an ENV directive, an API key baked into a config file — travels straight to your runtime environment. Unlike source code, image layers are often overlooked in security reviews, making them a prime vector for credential exposure.
With Red Hat Quay joining Docker Hub, Amazon ECR, Azure Container Registry, Google Artifact Registry, and JFrog Container Registry, GitGuardian now covers six major container registries — giving you unified secrets detection wherever your images live.
Get Started Today!
- Navigate to Settings > Integrations > Sources
- Click Install next to Red Hat Quay in the Container registries section
- Create an OAuth Application in your Quay instance and connect it to GitGuardian
This feature is currently available in beta. Check out the full setup guide to learn more.
--
Enhancements
- Public API: Added endpoint to retrieve GitGuardian's egress IP addresses in CIDR notation for allowlisting in firewalls, network security groups, or other access control systems. Learn more.