Flag admin and overprivileged NHIs across AWS, Entra, and Okta
Release Date: April 16, 2026
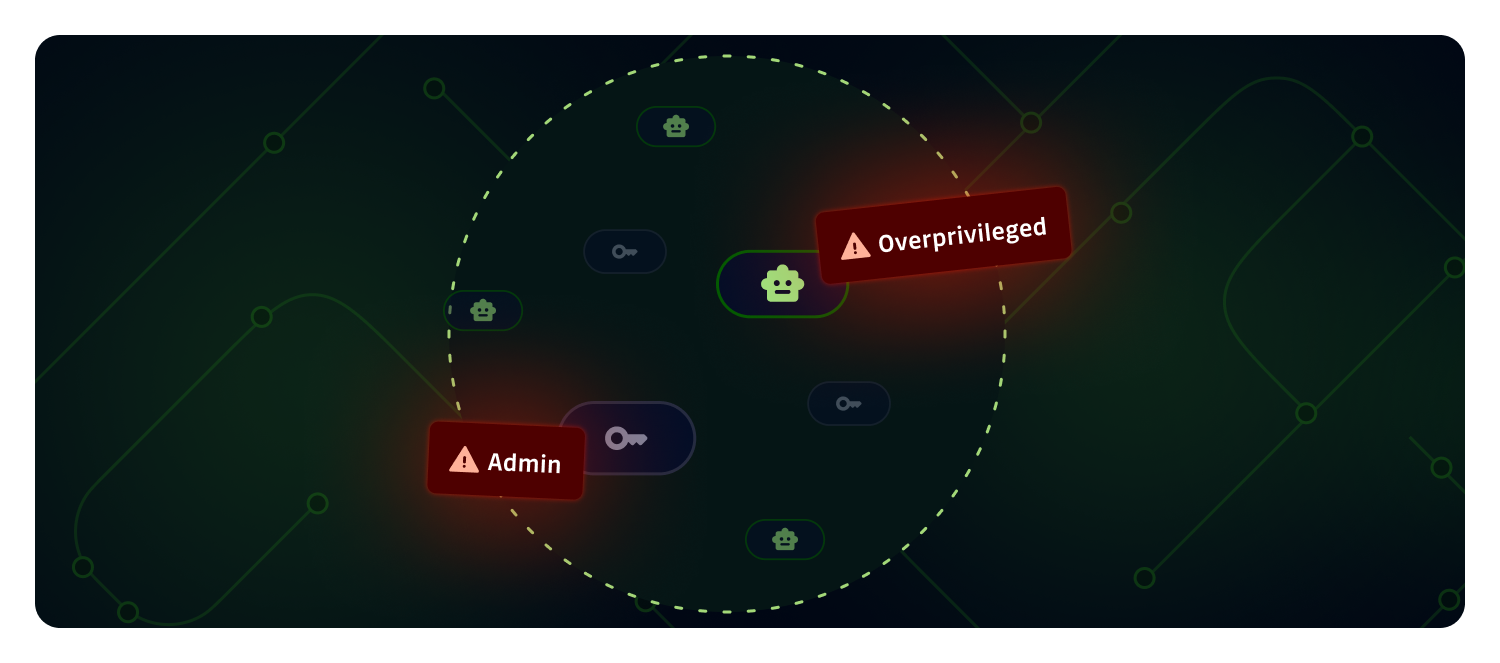
NHI Governance can now tell you which of your Non-Human Identities hold admin rights, which are overprivileged compared to what they need, and automatically raises the risk level of any policy breach that lands on an admin NHI. You get a prioritized inventory where the identities an attacker would abuse first are already at the top, across AWS IAM, Microsoft Entra, and Okta.
What does this mean for you?
- Admin identities at a glance: NHIs with admin-level permissions (e.g. AWS
AdministratorAccess, Entra Global Administrator, Okta Super Admin) are marked with an Identity level: Admin badge in the inventory and detail view. - New policy, Overprivileged Identity: A dedicated policy flags identities granted broader permissions than they use, so you can drive NHIs back toward least privilege.
- Smarter risk criticality: Any policy breach on an admin NHI is automatically bumped one severity level higher, capped at critical. A leaked internal secret on an admin identity now shows as critical, not high.
- Cross-source coverage: Admin and overprivilege checks run on AWS IAM, Microsoft Entra (directory roles, Azure RBAC, Microsoft Graph permissions), and Okta (built-in and custom admin roles).
Why is it important?
Not all NHIs carry the same risk. An admin or overprivileged identity that leaks gives an attacker full control of the account, tenant, or directory, while a scoped identity limits the blast radius to one system. Until now, spotting those identities meant combing through IAM policies, directory roles, and custom permissions by hand, and a leaked internal secret looked the same whether it belonged to a read-only service or a Global Administrator.
With this release you can:
- Focus remediation where it matters: Start with admin and overprivileged NHIs, and with the incidents their breaches generate, instead of treating every NHI equally.
- Enforce least privilege: Surface NHIs that accumulated broad permissions over time and bring them back in line.
- Shrink the blast radius: Cut the number of high-impact identities that a single compromised secret could abuse.
- Meet audit expectations: Evidence that admin and overprivileged machine identities are reviewed, named, and tracked.
Get started
- Open NHI Governance → Identities and sort by Risk criticality to see which NHIs rank highest.
- Use the Identity level filter to isolate admin NHIs, and the Breached policies filter to find Overprivileged Identity breaches.
- Learn more about admin identities, the Overprivileged Identity policy, and risk criticality.
This feature is available to NHI Governance paying customers.
Enhancements
- Privacy Mode: Workspace owners can now enforce privacy mode at the workspace level, restricting the ability to view plaintext secrets to managers only or owners only for tighter control over sensitive data visibility. Learn more.
- Audit Logs: The list of captured audit log event types is now available through the public API, making it easier to configure SIEM ingestion and alerting rules. Learn more.
- AI: Workspace admins can now manage third-party LLM usage directly from the dashboard. Choose between GitGuardian's managed LLM providers (default), routing calls through your own AWS Bedrock account with Bring Your Own Cloud, or turning external LLMs off entirely. Internal ML models for false positive detection, prioritization scoring, and similar issues continue to run regardless, and existing configurations are unchanged. Learn more.
Fixes
- Incidents: Fixed an issue where secret grasper matches found in long diffs were not visible in the dashboard occurrence view. The full file content is now displayed when the match falls outside the truncated patch.
- GitLab health check: Updated the GitLab instance health check for compatibility with GitLab.com and upcoming GitLab 19 self-hosted versions.